How AMC works for networking products:
In today’s competitive life everyone look for good quality products. Quality and Maintenance are the main things for products like laptops, desktops, printers, servers and other networking products. Usually there are two types for maintaining the products:
- AMC – Annual Maintenance contract
- CMC – comprehensive maintenance contract
AMC stands for Annual Maintenance contract: A manufacture company’s will provide the services through AMC by themselves or with the help of service providers. The contract will be for the period of 1 year and can be extended up to 3 years or 3 to 5 years as per the mutual understanding of the parties.Basically the service providers will provide only service support and would charge separately for every part under AMC. Sometimes in some cases few parts can be replaced during the visit by service engineer when it is mentioned in AMC contract that limited parts will be replaced.
 AMC for laptops,desktops and printers:
AMC for laptops,desktops and printers:
. Software and hardware installation
. Virus removal
. Data backup and recovery
. Spyware removal
. Wired and wireless networking
Essential components for AMC:
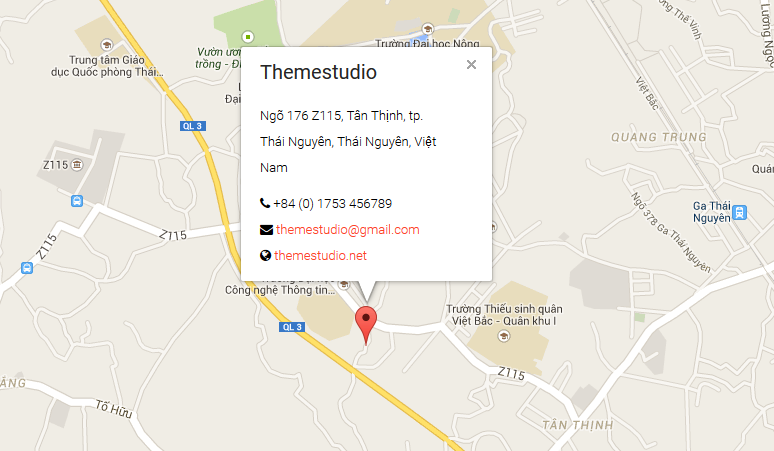
- Name and address of both the parties
- Cost of the contract
- Duration of contract
- Details of the equipment under contract
- Number of visits and breakdown call by the service engineer
- Payment terms
- Penalty clause
- Termination
- Signature
- Seal
Network Setup and Configurations: Companies with advanced network configurations can configure multiple IP addresses on the appliance’s Ethernet ports. Using multiple ports can enhance security or enable connections over non-standard networks. For example, if employees are restricted from accessing the Internet but need to provide off-network support, using one port for your internal private network and another for the public internet would allow world-wide users to request support without breaching your network security policies.
Security System Solutions, server implementations:
every system security is the main problem to recover the security system problem first Your website is protected from malicious traffic with Stack Path’s Web Application Firewall (WAF) integrated in every Secure CDN plan.Create custom rules to protect against OWASP threats, IP reputation, behavioral filtering and more. Downloadable raw logs for historical analysis.The primary function of a web server is to store, process and deliver web pages to clients. The communication between client and server takes place using the Hypertext Transfer Protocol (HTTP). Pages delivered are most frequently HTML documents, which may include images, style sheets and scripts in addition to text content.Multiple web servers may be used for a high traffic website, here Dell servers are installed together being used for the Wikimedia Foundation. A user agent, commonly a web browser or web crawler, initiates communication by making a request for a specific resource using HTTP and the server responds with the content of that resource or an error message if unable to do so. The resource is typically a real file on the server’s secondary storage, but this is not necessarily the case and depends on how the web server is implemented.While the primary function is to serve content, a full implementation of HTTP also includes ways of receiving content from clients. This feature is used for submitting web forms, including uploading of files.
Desktop/Laptop sales/Repairs:
Computer and laptops repair technicians and work in a variety of environments and different types, covering both the public and private sectors. A repair technician can Work in a corporate information technology department, in a central service center or in a retail environment of computer sales or any other service or in a public sector. The technician may work in the military, national security or law enforcement communities, health or public safety field, or an educational institution. In spite of the wide variety of working environments, all computer technicians perform similar physical and investigative processes, including technical support. Experienced technicians could specialize in fields such as data recovery, systems management or information systems. Some technicians are self-employed in a regional area. Some are outsourced as freelancers or consultants. This type of technician ranges from amateurs and a little money aside, for those who work professionally in the field. Computer malfunctions can range from a minor setting that is incorrect, to spyware, to viruses.As for the replacement of hardware and an entire operating system. Some technicians provide on-site services, usually at an hourly rate. Others may provide off-site services, Where the customer can leave it in the repair shop. Some have pick up and drop off services for convenient. Some technicians may also remove equipment recycling.